There are many various software application applications in the modern world, and the source code of one of most of them is hidden from our sight. But there are a variety of situations when we do require to comprehend the logic of working of platforms and applications, their algorithms, and specifics. That is where the Reverse Engineering Tools comes into the picture. There are many Free Reverse Engineering Tools/ Software that you can use according to your requirements or simply hire someone who provides reverse engineering services.

There are a lot of products to make this job easier. We are going to discuss some of the best reverse engineering software applications; primarily it will be reverse engineering tools for Windows. It’s hard to call the best software application reverse engineering tool– there many of them, and each one deals with some specific job of the multistep reversing procedure.
IDA
IDA stands for Interactive DisAssembler and it is undoubtedly among the best tools used in reverse engineering. It is mainly a disassembler for various formats of binary files but its numerous built-in features such as decompiler, hex editor, and debugger make it an all-in-one tool for analysis and reverse engineering.
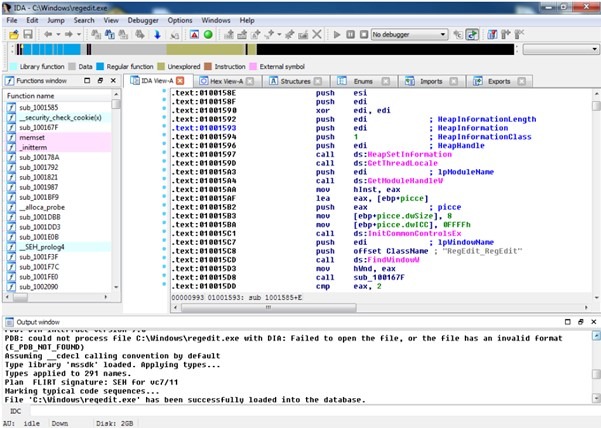
It is compatible with Windows, Mac OS X, and Linux platforms and can be used for the analysis of over 60 types of processors. It also comes with support for plug-ins that additionally enhance its functionality and the Hex-Rays decompiler is the most popular plugin for IDA.
Also Read- 5 Best Resources to learn & Get Programming Certifications for Free
UPX
UPX is an executable packer that achieves an excellent compression ratio and offers very fast decompression. It is an open-source free to use tool and since it is written using C++ and Assembly language, it is quite portable and delivers high performance.

UPX is very extendable and its class-based layout allows for the easy addition of new executable formats and new compression algorithms. The tool performs in-place decompression resulting in no memory overhead for your compressed executables.
DIE
DIE stands for Detect It Easy and is a free cross-platform tool to analyze files you load into the application and display detailed file information to detect the kind of protection applied to the binary code so that you can easily find a solution for removing it.
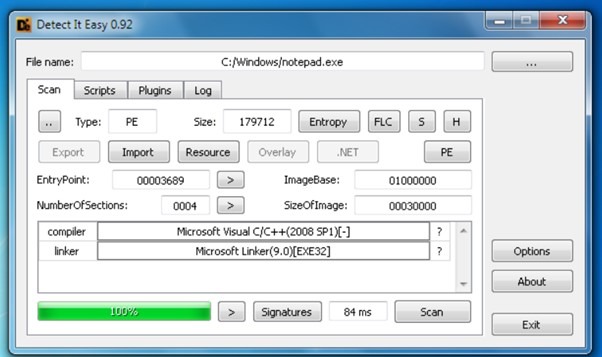
DIE supports over 200 file types for analysis. It can easily detect the compiler and linker used and it has been designed specifically to reveal file signatures and how they are packed so as to gather other information about files.
HIEW
Hex editors are a must-have reverse engineering tool and HIEW is one of the most used hex editors that allow you to modify any binary file. It comes with many built-in features such as a built-in 64-bit calculator, disassembler for x86, x86-64, and ARM, as well as an assembler for x86, x86-64.

It is a console-based application with a vast user database developed since 1991 with updates that are regular. The combination of the built-in disassembler and assembler allows users to navigate through the code and easily modify existing instructions.
Also Read- 11 Most Useful Google Chrome Extensions for Programmers
ILSPY
Distributed under the MIT License, ILSPY is an assembly browser and decompiler that works on the .NET platform. It is a great tool for decompilation of the whole-project as well as decompilation to C# and it can also work as a decompiler for BAML to XAML.
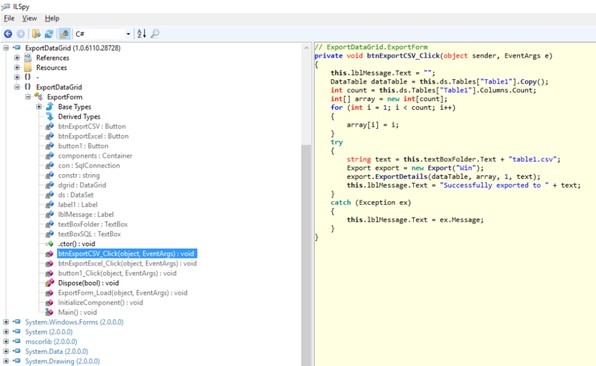
The Hyperlink-based navigation system allows users to easily find required files in the loaded application. The latest version of the ILSPY application is ILSpy 6.2.1.
DNSPY
DNSPY is a debugger, a .NET assembly editor, and the best reverse engineering tool for any .NET binaries. It can be used to debug .NET Framework, .NET Core, and Unity game assemblies without the requirement of any source code.

DNSPY comes with a built-in IL code editor and a debugger that provides high performance and high speed. It has a fairly intuitive and modern interface design and also offers the feature of light and dark themes.
X64DBG
The X64DBG debugger has set new standards in debugging software on the Windows platforms. This open-source tool comes with separate versions for 32-bit and 64-bit systems along with a large number of plugins, visual themes, and regular upgrades.
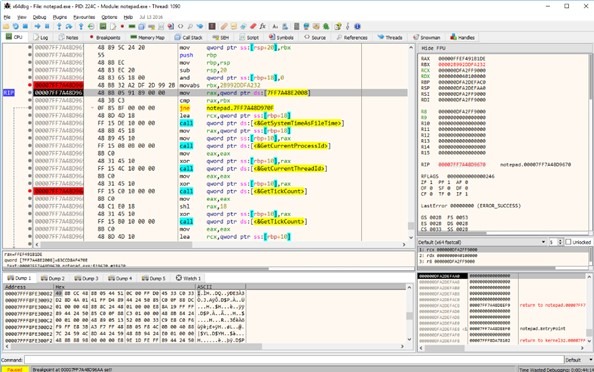
It can debug applications with the help of a single interface using an integrated, debuggable, ASM-like scripting language. Its internal engine is based on modern programming libraries such as TitanEngine, Capstone Engine, Keystone Engine. Using C++ and Qt X64DBG adds new features very quickly.
Also Read- Best Ways to Free Google Drive Storage Space in 5 Mins
DE4DOT
Written in C#, DE4DOT is a de-obfuscator and unpacker that can be used to restore a packed and obfuscated assembly to almost the original assembly. It can decrypt strings dynamically or statically and even decrypt other constants. Obfuscation is the process of purposefully creating machine code which is difficult for humans to understand.
Depending on what obfuscator was used to obfuscate an assembly, it can remove the tamper detection code and anti-debug code. It also removes most of the junk classes added by the obfuscator.
ANTINET
ANTINET is a reverse engineering tool that can be used to prevent a managed .NET debugger or profiler from working by using the undocumented features of Microsoft’s CLR.

A managed .NET debugger gets debug messages from the .NET debugger thread. ANTINET program kills the .NET debugger thread thereby resulting in no debug messages being passed to the managed .NET debugger due to which it will fail to work.
Also Read- How to Get Github Student Developer Pack in 2020
PROCYON
Developed by Mike Strobel, Procyon is a popular open-source Java Decompiler. Most of the decompilers cannot handle enhancements from Java 5 and beyond but Procyon can easily handle such enhancements making it excel in areas where others fall short. It works well with enum declarations, enum and string switch statements, annotations, java 8 lambdas, and method references.

Procyon decompiler reads the program binaries, decompiles them, infers data types, and emits structured java source code, in short, it can decompile .class File to .java File in no time.
ANDROGUARD:
Python language is highly suited for reverse engineering since it has a relatively simpler syntax and allows for quick and easy actions. Androguard is one such python-based tool that provides reverse engineering and malware analysis services for the Android platform. It is available for Linux, Windows, and OSX platforms.
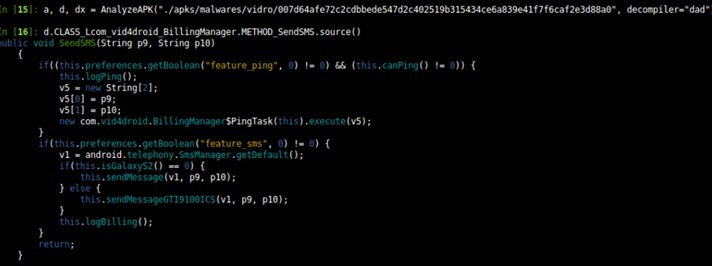
It can be used to manipulate many file-formats including DEX, ODEX, APK, Android’s binary XML (AXML), and Android Resources (ARSC). Androguard provides access to static analysis of code and allows for the creation of your own static analysis tool.
It is very helpful for Android developers since using this tool they can determine if an application has been pirated, check if the android application is present in a database, and even transform Android’s binary XML into classic XML.
SANDBOXIE
The process of sandboxing is very popular while reverse engineering an application and Sandboxie is a software that creates a virtual sandbox for applications that you want to run.
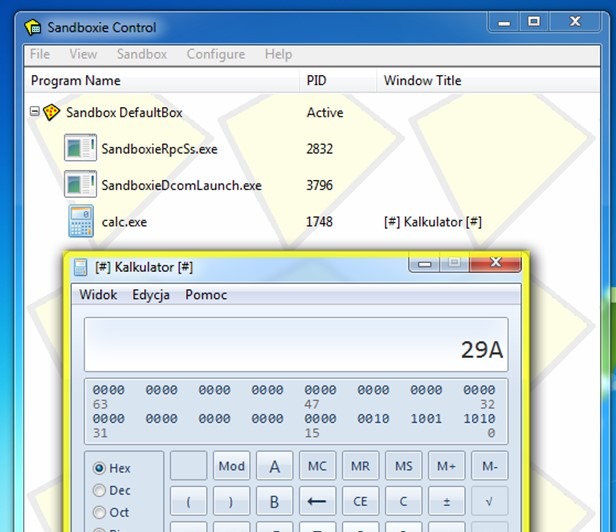
It is an open-source tool available for Windows platform only. It is very helpful in situations where you have certain untrusted code and you want to test it. Using Sandboxie, you can run the unknown code in a sandboxed process, without the fear of damaging your system since all operations within the virtual sandbox are isolated and have no influence over the system.
Resource Hacker
Resource Hacker is a resource editor with fast processing speed that can be used to find raw binary data, dialogs, bitmaps, strings, icons, etc. It is available for both 32-bit and 64-bit Windows applications and can manipulate data on script language resource level.

Although it is mainly a GUI-based application, it also provides several options for compiling and decompiling resources from the command-line interface.
The process of reverse engineering is not a single step process and the above-mentioned are some of the many tools available in the market that resolve a particular task of this multi-step reversing process. It is with the combined help of these tools that you can complete the reverse engineering of a particular application and thus, it is very important to have tools relating to all tasks in your toolkit.
Also Read- 10 Best Tools to Stay Anonymous from Hackers on Internet









